Delve Got Caught Faking Compliance. We Chose the Slow Way on Purpose.
The Delve scandal is exposing what happens when compliance becomes a product to ship fast rather than a promise to keep. At anyformat, we took the opposite path, and it's taking us months. On purpose.
If you work in tech and have been online this week, you've probably seen the Delve story unfolding in real time.
A whistleblower known as "DeepDelver" published a detailed investigation alleging that Delve, a YC-backed compliance automation startup valued at $300 million, had been systematically misleading hundreds of customers into believing they were compliant with SOC 2, HIPAA, ISO 27001, and GDPR. The allegations are severe: fabricated evidence of security controls that were never implemented, auditor conclusions generated before any independent review took place, and trust pages listing measures that simply did not exist.
TechCrunch picked it up. Inc. covered it. Insight Partners, the firm that led Delve's $32 million Series A, quietly scrubbed its investment thesis article from the web. Companies like Lovable have already publicly distanced themselves.
Delve denies the accusations. They say they're an automation platform, not an audit firm, and that templates are standard industry practice.
But the damage is already structural. Regardless of how the Delve story resolves, it has cracked open a question that every enterprise buyer should be asking: When your vendor shows you a compliance badge, what does it actually mean?
The real problem is bigger than one startup
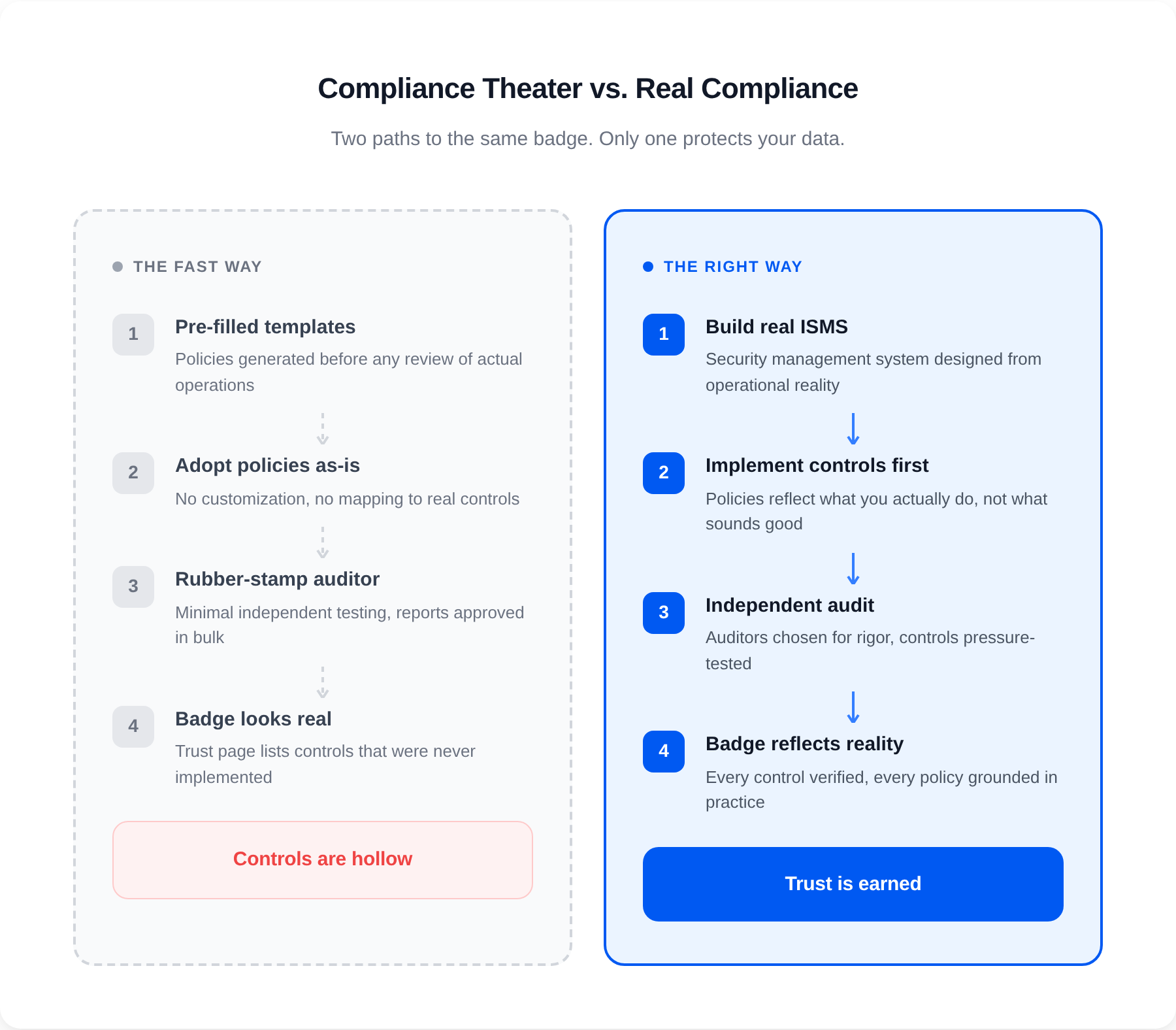
The Delve situation is dramatic, but the pattern it exposes is not new. It has a name: compliance theater.
Compliance theater is what happens when the process of getting certified becomes more important than the security posture the certification is supposed to represent. When the badge becomes the product instead of a byproduct of doing things right.
The compliance automation market has grown rapidly because the pain it addresses is real. Getting SOC 2 or ISO 27001 certified the traditional way is slow, manual, and expensive. Startups that promise to compress that timeline from months to days are naturally attractive. But speed and rigor exist in tension. And when a platform optimizes purely for speed, something has to give.
What gives, typically, is the substance underneath the stamp.
Pre-filled evidence that documents processes nobody actually implemented. Audit firms that approve reports without meaningful independent testing. Trust pages that list security measures as fact when they are aspirational at best.
The result: companies walking around with a badge that says "certified" while the underlying controls are hollow. Their customers, partners, and regulators trust that badge. Until something breaks.
Why this matters if you work with document intelligence
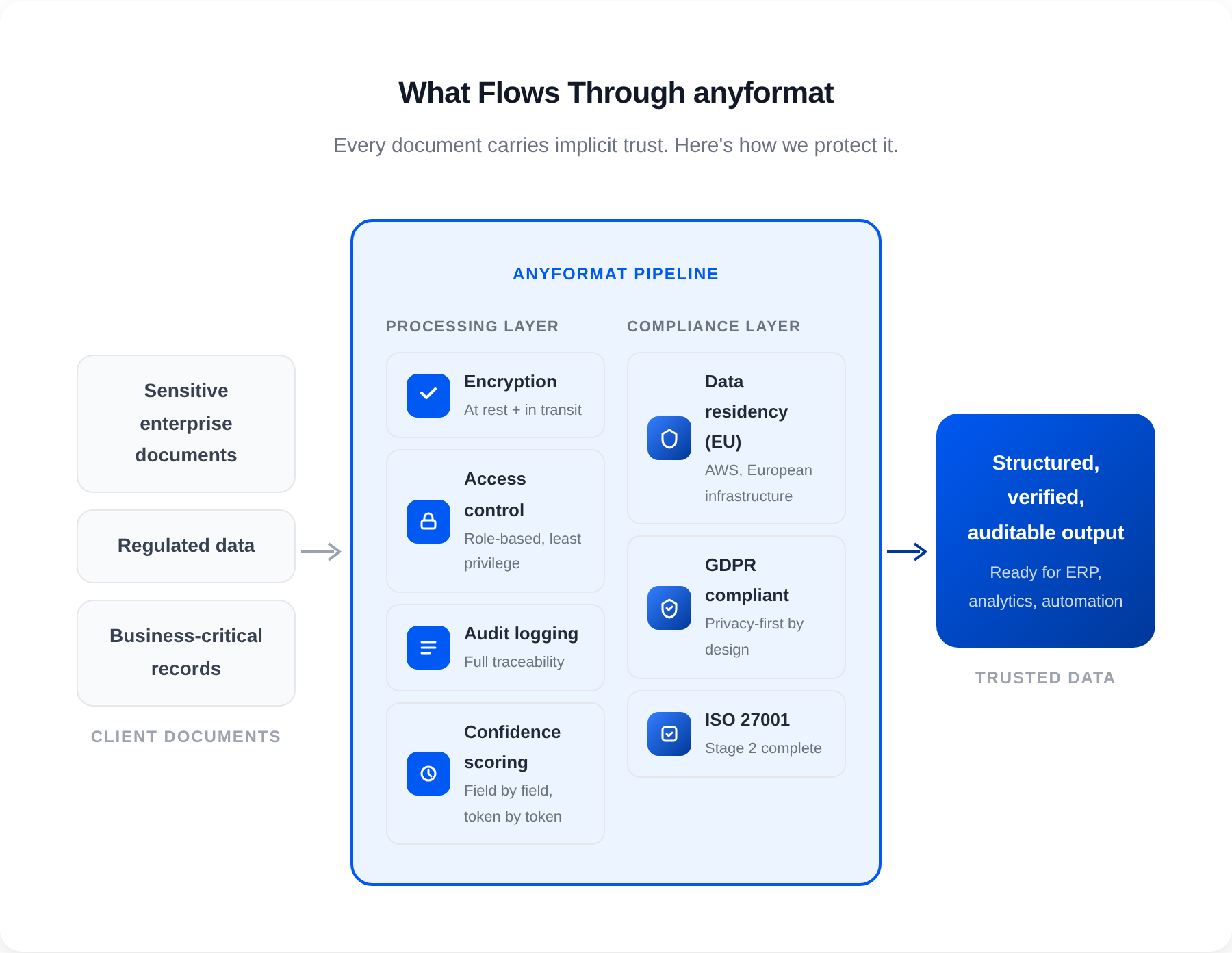
If you process sensitive enterprise documents, the compliance posture of your tooling is not a checkbox. It is a load-bearing wall.
Every document that flows through a platform like anyformat carries implicit trust. A client sending us their most sensitive business records is not just sharing data. They are sharing the operational and legal backbone of their business.
If our compliance certifications were hollow, that trust would be a lie. And unlike a product bug you can patch, broken trust in regulated industries compounds: contractual liability, regulatory fines (up to 4% of global revenue under GDPR), criminal exposure under HIPAA, and reputational damage that no PR response can repair.
This is why we refuse to treat compliance as something to "get through."
How we chose to do it at anyformat
We are currently in the final stages of ISO 27001 certification. Stage 2 of the audit is complete. We are close to the finish line.
But here's the part that matters: we have been at this for months. Not because we failed anything. Not because we got stuck. Because we chose to do it at a pace that ensures every control, every policy, every procedure reflects what we actually do, not what looks good on paper.
That was a deliberate decision and, honestly, not always a comfortable one. When competitors can wave a certification in front of prospects while you're still deep in the process, the temptation to cut corners is real. We've seen what "fast compliance" looks like now. We would rather be late and legitimate than early and empty.
Here's what that looks like in practice:
We built our ISMS before we built the audit narrative. Our Information Security Management System was not assembled to satisfy an auditor's checklist. It was designed to protect the data our clients entrust to us. The policies came from our actual operational reality, not from templates we adopted wholesale.
We run a privacy-first architecture, not a privacy-first slide deck. anyformat is deployed on AWS with data residency controls, encryption at rest and in transit, strict access controls, and audit logging across the entire document processing pipeline. These are not features we added for the certification. They are the foundation we built the product on. Being EU-rooted is not a marketing angle for us. It is a regulatory obligation and a competitive advantage we take seriously.
We chose auditors for rigor, not for speed. We did not optimize for the fastest path to a certificate. We selected an audit process that would pressure-test our controls, challenge our assumptions, and surface real gaps. Because discovering a gap during an audit is a gift. Discovering it after a breach is a disaster.
Our confidence scoring is part of our compliance story. When anyformat extracts data from a document, every output comes with a confidence score: field by field, token by token. This is not just a product feature. It is an architectural commitment to transparency and auditability. If we are going to ask enterprises to trust our outputs, we owe them the ability to verify that trust at the most granular level.
What to ask your vendors (including us)
The Delve scandal will fade from the news cycle eventually. But the questions it raises should become permanent fixtures in every procurement and security review:
"Can I see the scope of your certification?" A SOC 2 or ISO 27001 certificate is only meaningful within its defined scope. If the scope is narrow or excludes the systems that actually process your data, the badge is decorative.
"Who conducted the audit, and what is their accreditation?" Not all audit firms are equal. Independence, accreditation, and peer review status matter. Ask. Verify.
"Can you walk me through the controls, not just the report?" Any vendor should be able to explain, in plain language, what they actually do to protect your data. Not what a template says they do. What they do.
"How do you handle evidence collection: automated, manual, or pre-filled?" Automation is great when it collects real evidence from real systems. It is a problem when it generates the appearance of evidence for processes that don't exist.
"What happens when something fails?" Incident response, breach notification timelines, recovery procedures. The answer to this question tells you more about a company's security maturity than any trust page ever will.
Ask us these questions. Seriously. We would rather have a hard conversation during procurement than an impossible one after an incident.
Certifications are not stamps. They are promises.
There is a version of this blog post that would be easier to write. One where we simply say "we're not like Delve" and move on.
But that would miss the point.
The Delve story is a symptom of an industry-wide problem: compliance has been productized to the point where the certification itself has been decoupled from the security it is supposed to represent. When you can get a SOC 2 report in days, powered by pre-filled evidence and rubber-stamped by auditors who never independently test your controls, the entire trust framework collapses.
At anyformat, we process some of the most sensitive documents our clients have. Documents that drive decisions, trigger payments, and carry regulatory weight. We don't get to treat compliance as a growth hack. For us, it is the infrastructure on which everything else depends.
Our ISO 27001 certification is taking us months because we are building something that will hold up under scrutiny. Not just the auditor's scrutiny. Our clients' scrutiny. And our own.
Because a certification that doesn't reflect reality isn't a certification. It's a liability.
See how anyformat's compliance compares: vs Reducto · vs Extend AI · vs Nanonets · All comparisons →
anyformat is the document intelligence platform that turns unstructured documents into reliable, structured data, with enterprise-grade security, confidence scoring, and full auditability. We are GDPR-compliant and in the final stages of ISO 27001 certification. Learn more at anyformat.ai


